Platform Capabilities
This page provides an at-a-glance overview of the core capability areas of the Forward Enterprise platform. Each section highlights key functionality — for comprehensive details, configuration guidance, and advanced usage, refer to the corresponding sections in the product documentation.
Network Search
The platform provides advanced network search capabilities enabling operators to locate any network element, device, interface, route, or configuration construct across the entire managed network fabric using natural-language and structured queries with real-time results. For full details, see Search.
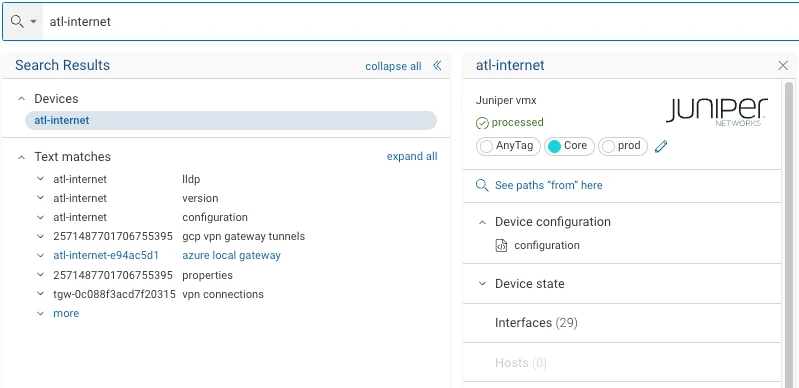
Supported query types:
- Device hostnames (e.g.,
atl-internet,sjc-app-lb01) - IPv4 addresses (e.g.,
10.117.101.7) - Interface identifiers (e.g.,
sjc-ce02 ge-0/0/12) - MAC addresses (e.g.,
50:00:00:4f:00:02) - Free-text strings, including exact-match phrases enclosed in quotation marks (e.g.,
"protocol isis") - Routing protocol keywords (e.g.,
ospf,bgp) - Scoped configuration queries using the
in:configmodifier
Search results are returned immediately, spanning the full network fabric including device configurations, interface data, addressing information, and protocol state.
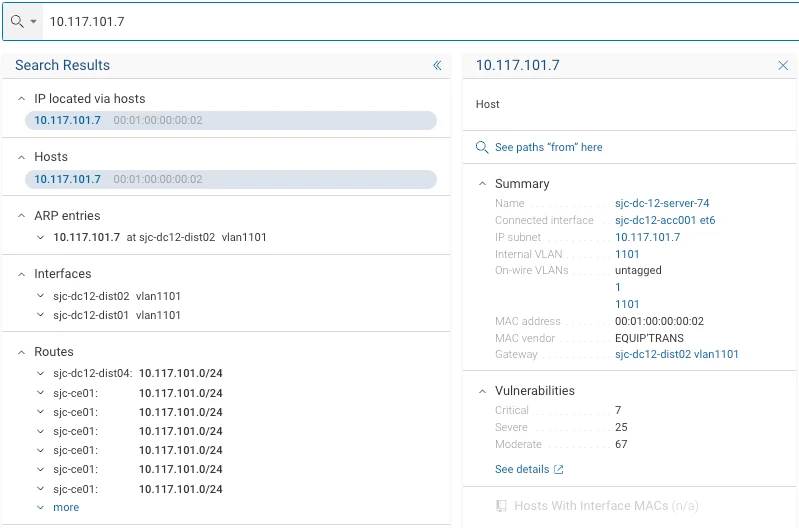
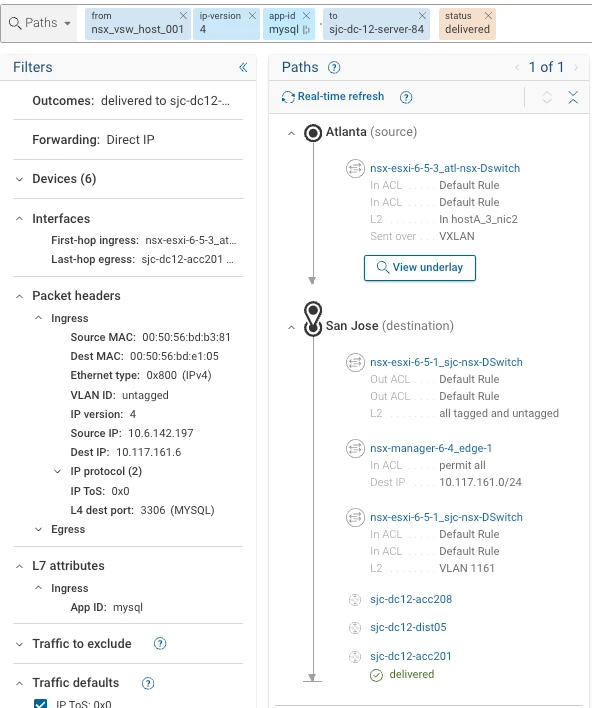
Path Search and Analysis
Forward Enterprise computes and visualizes all possible forwarding paths between any two endpoints across the network, including multi-hop, multi-protocol, and load-balanced paths. Path analysis accounts for ACLs, routing policies, NAT, and tunnels to deliver complete, accurate end-to-end reachability results. For full details, see Path Analysis.
Common search specification parameters include:
- Source endpoint or zone (e.g., internet-facing interfaces)
- Destination endpoint, IP address, or delivery state
- Layer 4 destination port, specified by number or well-known name (e.g., HTTPS)
- IPv4 destination address filters
- Device bypass and permit-all mode modifiers
Packet header filtering exposes an interactive filter panel where operators can enumerate all reachable Layer 4 destination ports and progressively narrow results by applying additional packet header field constraints (such as source/destination IP, protocol, and port).
Results are organized into path groups, each representing a distinct set of forwarding paths sharing common properties.
When a path traverses a firewall or policy enforcement point, Forward Enterprise displays the applicable ACL and NAT policies at each relevant hop, with the specific rules matched by the traffic profile highlighted.
Bypass mode allows a specified device to be excluded from the forwarding path computation, enabling operators to model alternate path behavior.
Permit-all mode instructs the path computation engine to disregard firewall deny rules, allowing operators to determine the forwarding path that would be taken if all security policies were permissive.
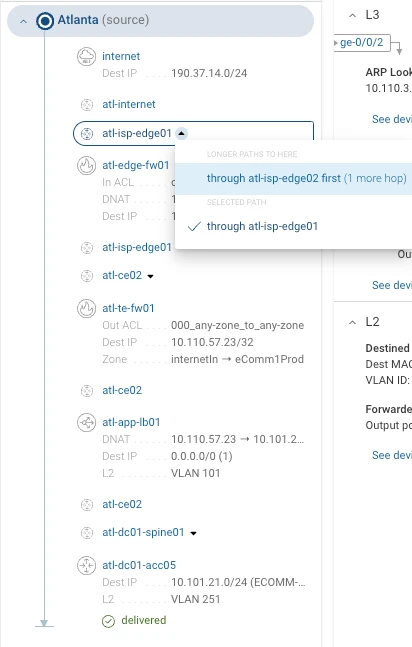
Intent Verification
The platform continuously verifies that observed network behavior conforms to operator-defined intent. Automated checks run against business policies, security requirements, and operational baselines, surfacing violations immediately without manual inspection. For full details on writing and managing verification checks, see NQE.
Operators define intent checks using a structured query syntax that expresses precise behavioral expectations. An
example verification targeting all network flows originating from the Internet and destined for 190.37.14.120,
excluding those using the HTTPS protocol, is expressed as:
f(internet)(ipv4_dst.190.37.14.120)(!tp_dst.HTTP)z(delivered)
Saved intent verifications are displayed and managed through the Verify application, which presents the current pass or fail status of all defined checks against live network state.
NQE-Based Verification
Forward Enterprise supports programmatic network verification via the Network Query Engine (NQE). Operators can author structured queries against a unified network model to assert correctness of any configuration or state attribute across all managed devices simultaneously.
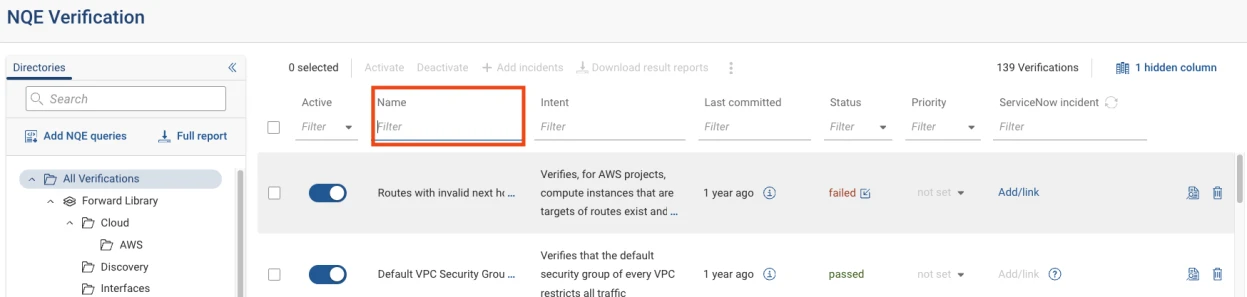
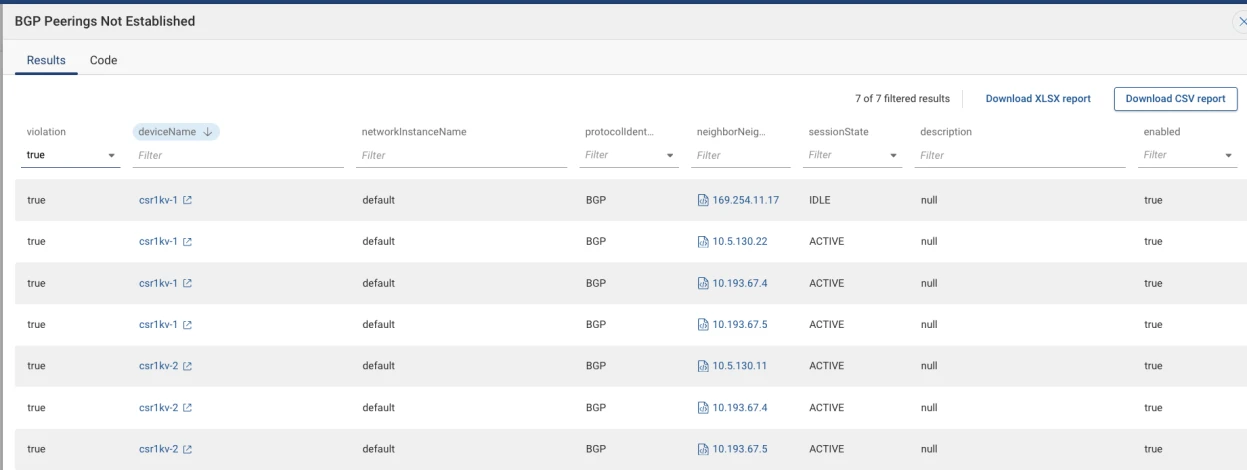
NQE Verification checks are accessible through the Verify application. Individual checks can be located and filtered by name within the check library. Check results are surfaced with pass/fail status, and failed results expose detailed per-device findings.
Key characteristics:
- Customizable checks tailored to specific network behaviors, configurations, and organizational policies
- Checks execute simultaneously across all managed devices within the network model
- NQE queries access configuration attributes, operational status, and performance metrics
- Verification checks run continuously and automatically
- Supports automated, ongoing verification against industry standards and internal policy requirements
- Identifies conditions that deviate from defined intent before they cause operational impact
NQE Query Library
Forward Enterprise ships a comprehensive, continuously maintained library of pre-built NQE queries covering security hardening, compliance frameworks, operational best practices, and vendor-specific checks, enabling immediate value without custom query development.
The library is divided into the Forward Library (read-only, shared across the organization) and the Org Repository (writable, organization-specific).
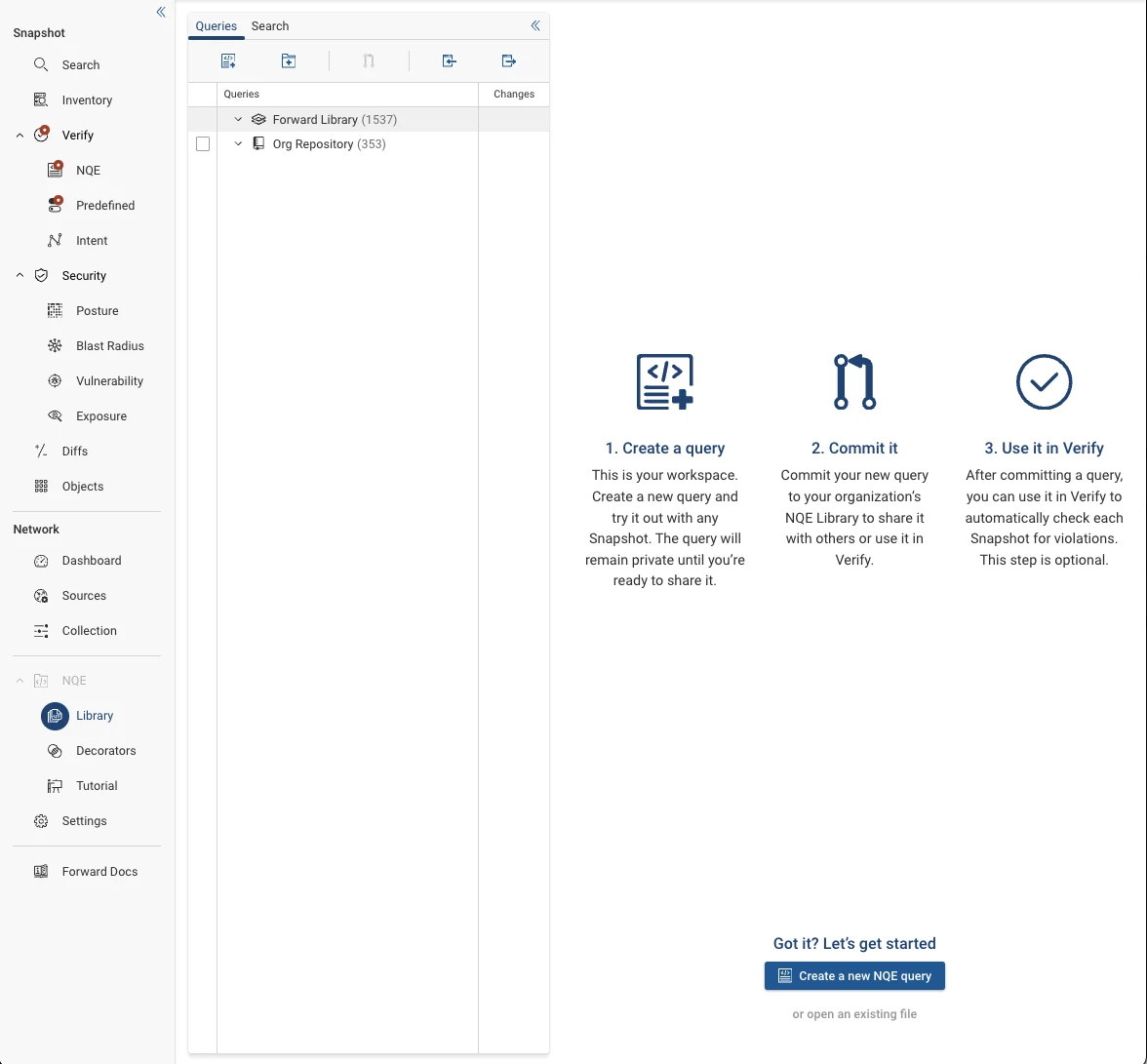
Library organization patterns:
- Users: top-level directory for all platform users
- Decorators: queries for generating UI decorators
- Library: routines that encourage code reuse
- Templates: global pattern matching templates
- Staging: directory for promoting queries to review and testing
- Verifications: queries associated with the Verify function
- Reports: queries associated with Inventory+ reports
- API: queries for programmatic access to external systems
- Integrations: queries for storing external data in NQE data types
- Synthetics: queries for managing Synthetic Devices
The NQE Library includes an integrated development environment (IDE) with access to the full NQE data model explorer.
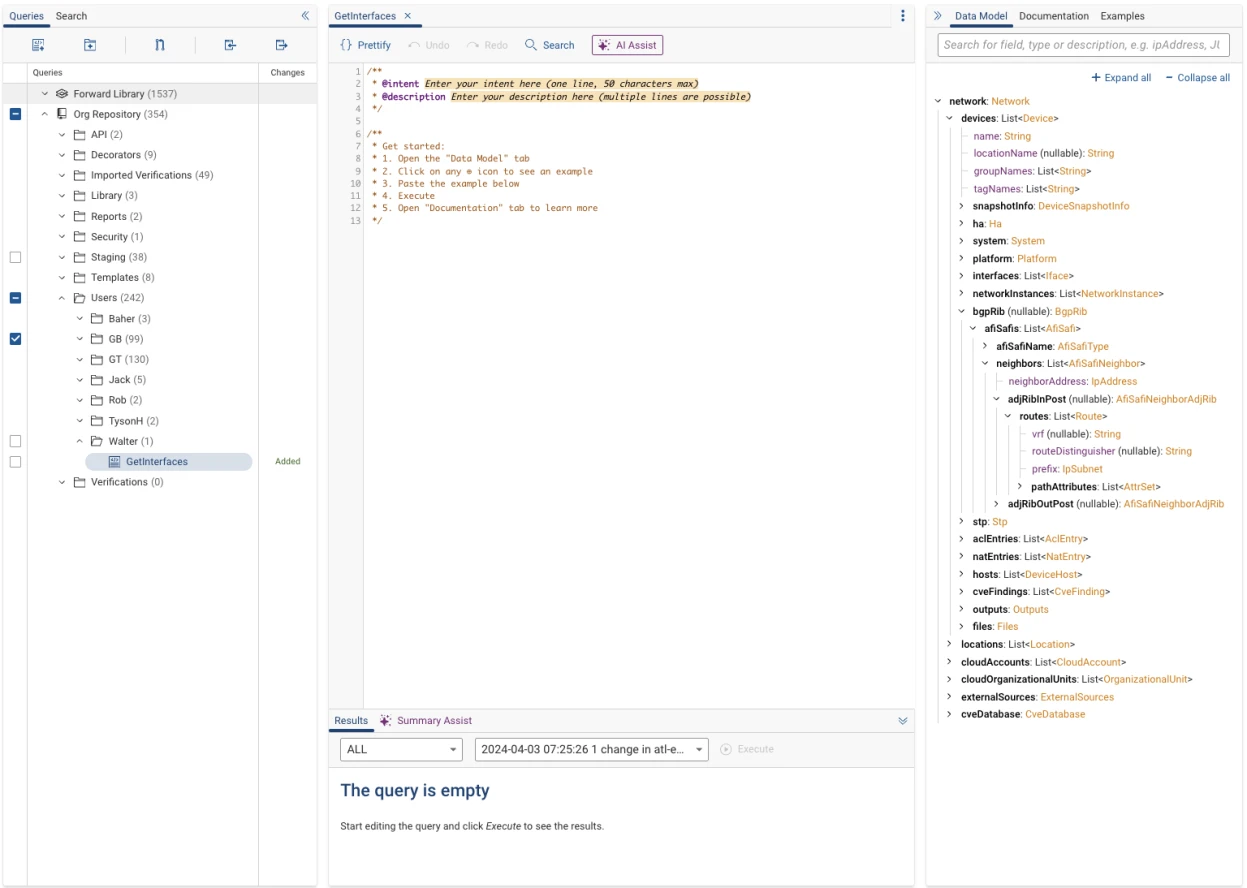
Newly created queries exist initially as drafts. The library incorporates version control integration, allowing queries to be committed and tracked through a change history.
Blast Radius Analysis
For full details, see Blast Radius.
The platform quantifies the operational blast radius of any network change, failure scenario, or security incident, identifying all downstream devices, services, and flows that would be affected, enabling risk-informed change management and incident response.
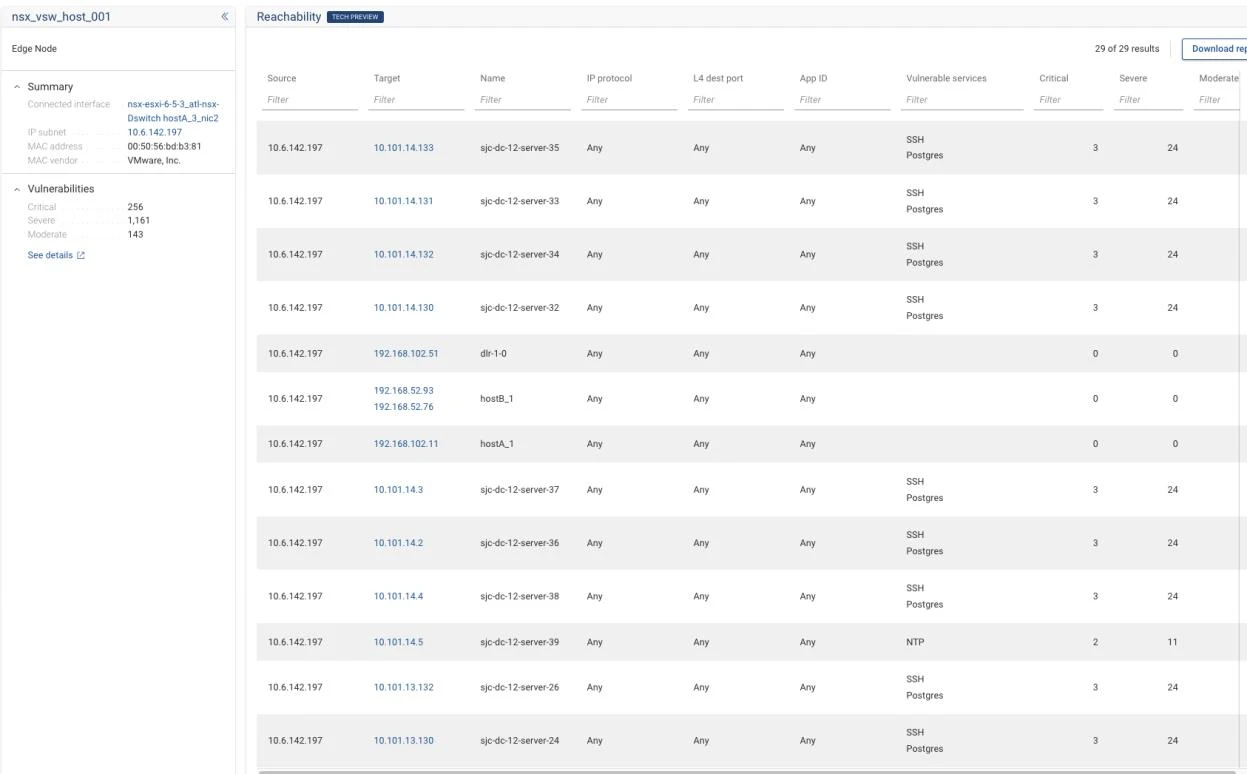
The Blast Radius function accepts a source host as input and enumerates all reachable destinations across the full network topology, reporting the protocols and ports over which connectivity exists. Hosts are flagged with vulnerable services detected on those reachable paths.
Results can be filtered by application identifier to isolate specific protocol-level connectivity (e.g., filtering by
mysql to confirm connectivity over a known vulnerable service).
Security use cases:
- Prioritization of vulnerability patching based on exploitability and reachability
- Identification of lateral movement pathways for network segmentation design
- Proactive threat hunting through detailed analysis of attacker traversal paths
- Comprehensive security posture assessment of the reachable attack surface
- Incident response scoping to bound the extent of a potential compromise
Network Inventory
For full details, see Inventory.
Forward Enterprise maintains a continuously updated, vendor-normalized inventory of all managed network devices, interfaces, software versions, and configuration state, providing a single authoritative source of truth for network asset management and audit.
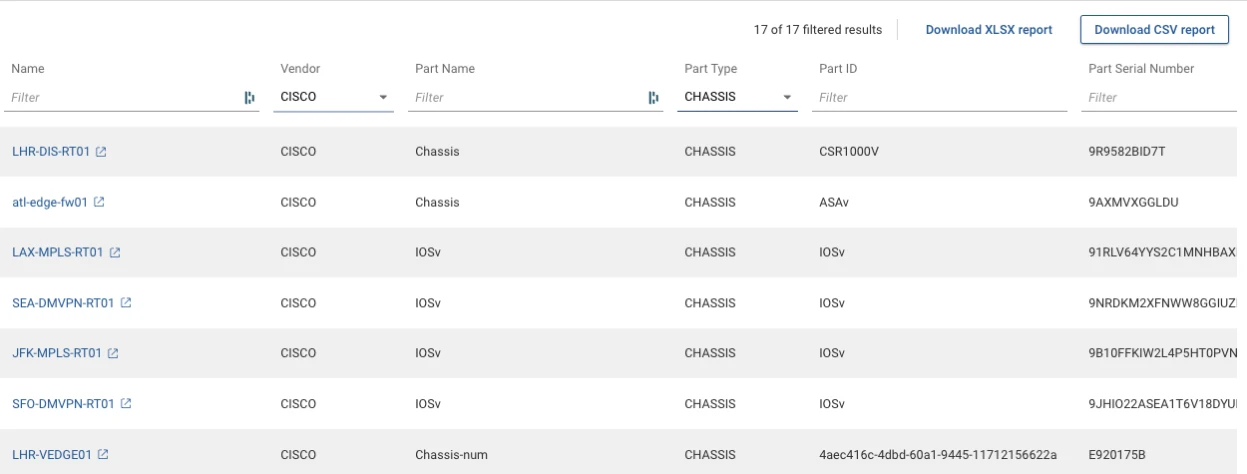
Inventory reporting capabilities:
- Custom reporting leveraging NQE queries for detailed analysis of device state, hardware attributes, and configuration
- Hardware inventory queries to retrieve structured hardware data filtered by vendor, component type, and other attributes
- Table-level filtering to refine large datasets to specific asset subsets
- Network insights providing visibility into vulnerabilities, hardware lifecycles, and subnet-level asset composition
- Custom reports can be saved and shared across team members
Security Posture Assessment
For full details, see Security Posture.
The platform performs continuous, automated assessment of network security posture by evaluating device configurations and network behavior against industry security frameworks and organizational policies.

The platform supports the creation of Security Zone Matrices, which define and evaluate network reachability across configured security zones. A matrix is constructed by selecting resource pools and associating specific network devices with all relevant zones. The matrix continuously assesses reachability across all configured source and destination zone pairs, presenting results through color-coded status indicators.
Capabilities:
- Automated reachability assessment across firewall zones, VRFs, and subnets
- Security Zone Matrix construction scoped to individual devices or groups of devices
- Color-coded status indicators for at-a-glance compliance review
- Detailed connectivity tables showing traffic flows between resource containers
- Enforcement point identification for paths within security zones
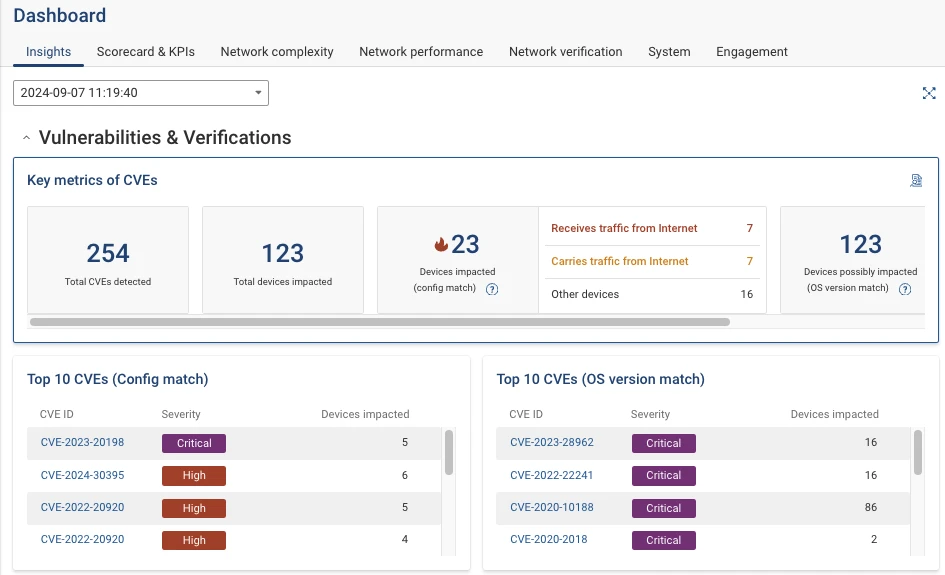
Vulnerability Analysis
Forward Enterprise correlates device inventory with published CVE databases to identify known vulnerabilities present in the network, reporting affected devices and software versions to enable prioritized remediation. The referenced CVE database is updated with each platform release. For full details, see Vulnerability Analysis.
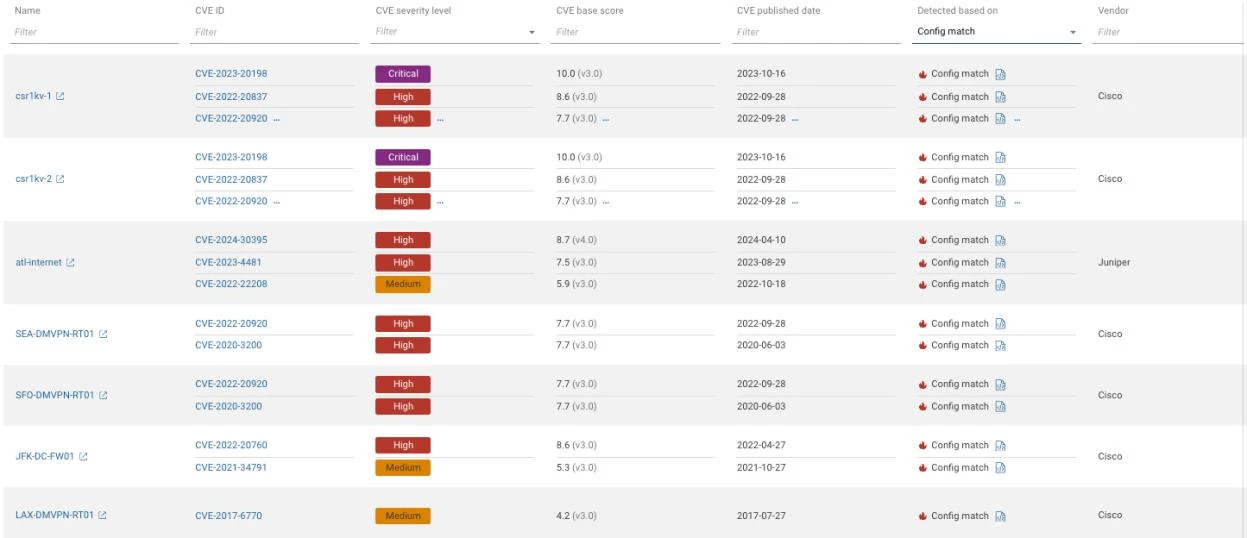
Vulnerabilities are presented in two view options: a Devices-centric view and a CVEs-centric view. The platform supports filtering by configuration match (confirmed exposure) and by internet reachability (external attack surface).
Key capabilities:
- Correlation of device inventory with the NIST CVE index
- Device-centric and CVE-centric views
- Filtering by configuration match to identify confirmed exposure
- Filtering by internet reachability to assess external attack surface
- Prioritization based on vulnerability severity and real-world exploitability
Exposure Analysis
For full details, see Exposure Analysis.
The platform determines network-layer exposure by computing which assets and services are reachable from any specified source, identifying unintended access paths, over-permissive ACLs, and lateral movement vectors.
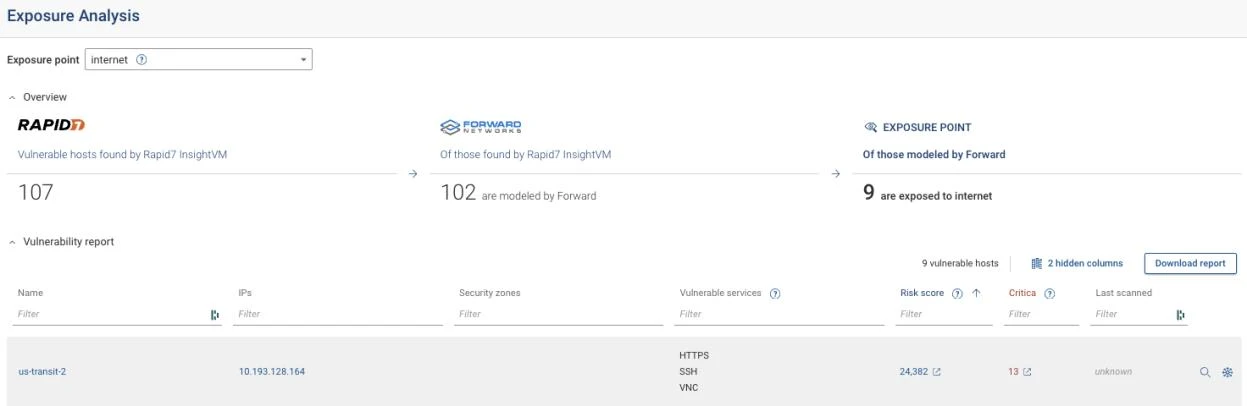
Forward Enterprise integrates host vulnerability data from Rapid7 and Tenable scanners with network-layer risk attributes.
The Exposure Analysis application provides:
- Total vulnerable hosts identified by connected scanning tools
- Total hosts modeled by the Forward Enterprise platform
- Detailed vulnerability reports with filtering by host name, IP address, vulnerable services, and criticality
- Connectivity details showing network-layer reachability and flow analysis for each host
- Blast radius analysis assessing potential spread of a vulnerability from a selected host
Topology Visualization
For full details, see Topology.
Forward Enterprise renders accurate, live network topology maps derived directly from device state rather than manual diagrams, providing always-current visibility into physical and logical connectivity across the entire network.
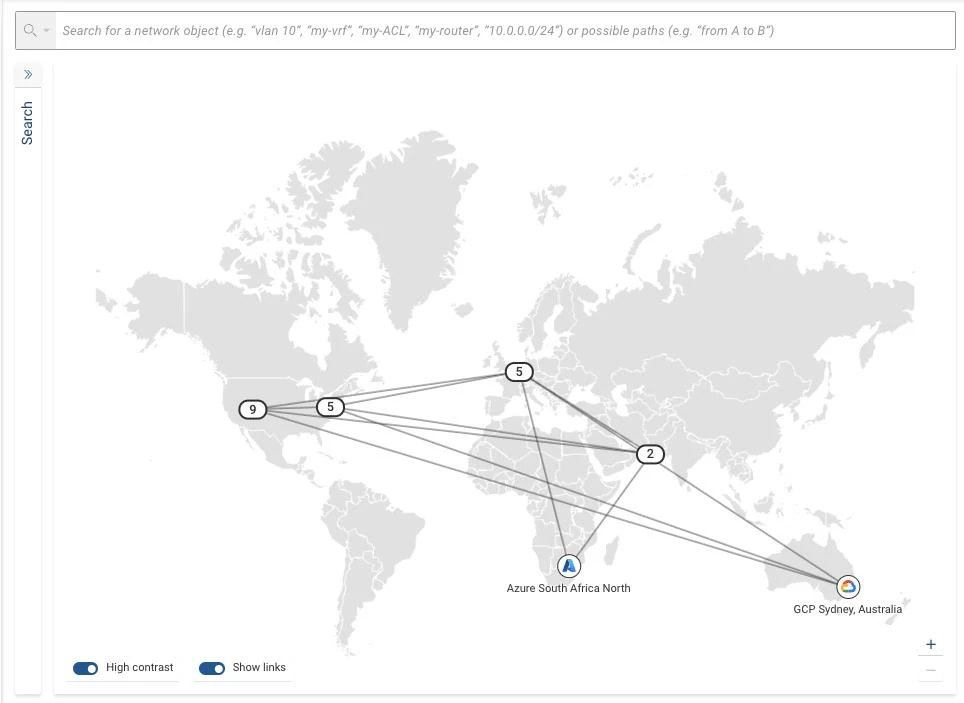
Supported topology layers:
- Physical topology: physical connections between devices, including device names, interface identifiers, and link states (UP, DOWN, one-way, no potential)
- Layer 2 (L2) topology: Layer 2 connectivity with VLAN-level filtering and per-link spanning tree states
- BGP topology: BGP neighbor relationships labeled with associated autonomous system numbers
- Layer 3 (L3) topology: Layer 3 network configurations with links annotated in CIDR notation
Topology views can be scoped to specific network locations or segments for focused analysis.
Operational Dashboards
For full details, see Dashboard.
The platform provides configurable dashboards that aggregate network health, compliance status, security posture, and operational metrics in a single interface, supporting both day-to-day operations and executive reporting.
The Dashboard is composed of discrete widgets, each representing a distinct aspect of network data or operational performance metrics. It surfaces indicators of network performance health (uptime, error rates, traffic pattern anomalies) and network complexity (device counts, connection topologies, configuration data).
Historical trend analysis provides verification success rates over time and patterns in user activity.
Diffs
Forward Enterprise captures point-in-time network snapshots and provides precise change detection between any two snapshots, delivering full visibility into what changed in device configuration or network state, when, and across which devices. For full details, see Diffs.
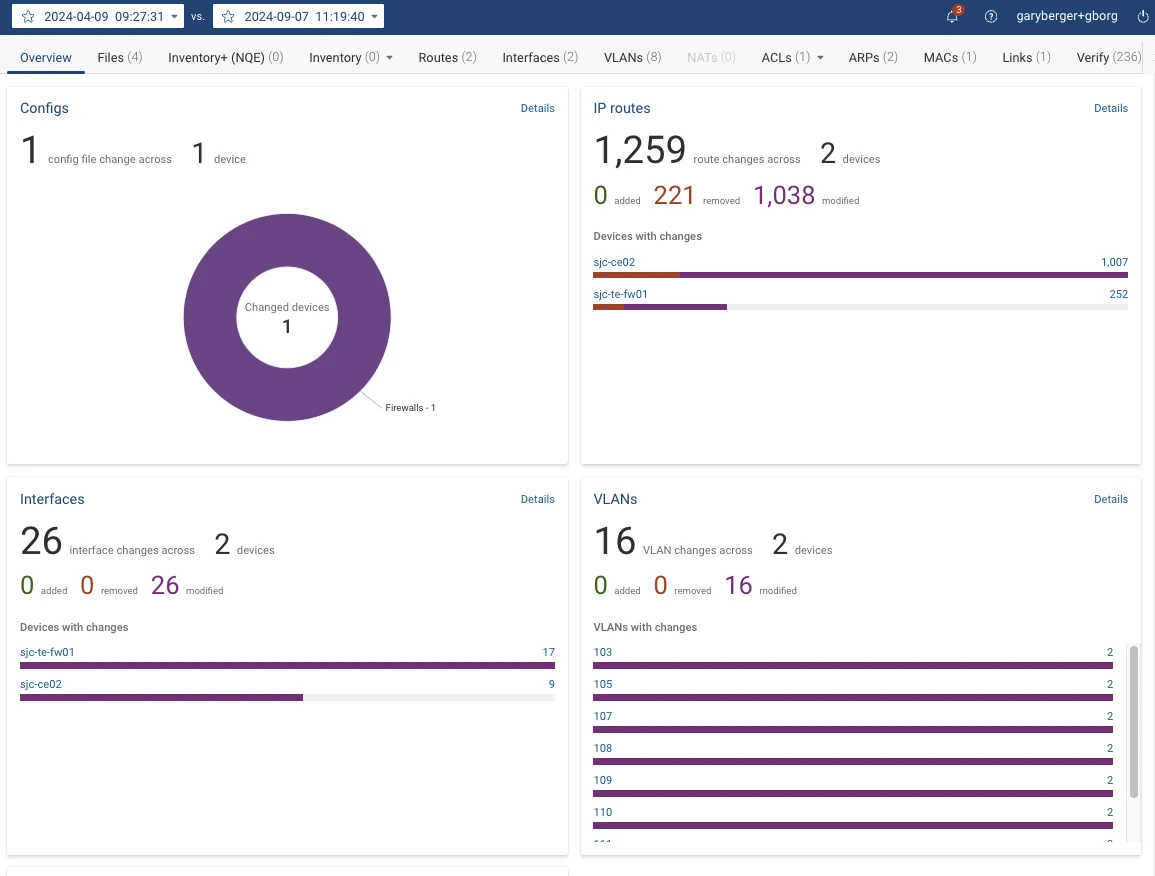
Scope of change detection:
- Network topology changes, including alterations to device adjacency and connectivity structure
- Layer 2 changes, including modifications to VLAN assignments and segmentation configuration
- Layer 3 changes, including alterations to routing configurations and traffic forwarding paths
- Security configuration changes, including modifications to ACL rules and NAT configurations
- Impact on network intent policies resulting from any of the above changes
Snapshot comparison is not limited to sequential snapshots; any two snapshots can be selected regardless of their position in time. The platform produces a unified diff across multiple network layers simultaneously.
Performance Analysis
The platform delivers network performance analysis enabling operators to identify utilization bottlenecks, assess capacity headroom, and evaluate the performance characteristics of forwarding paths.
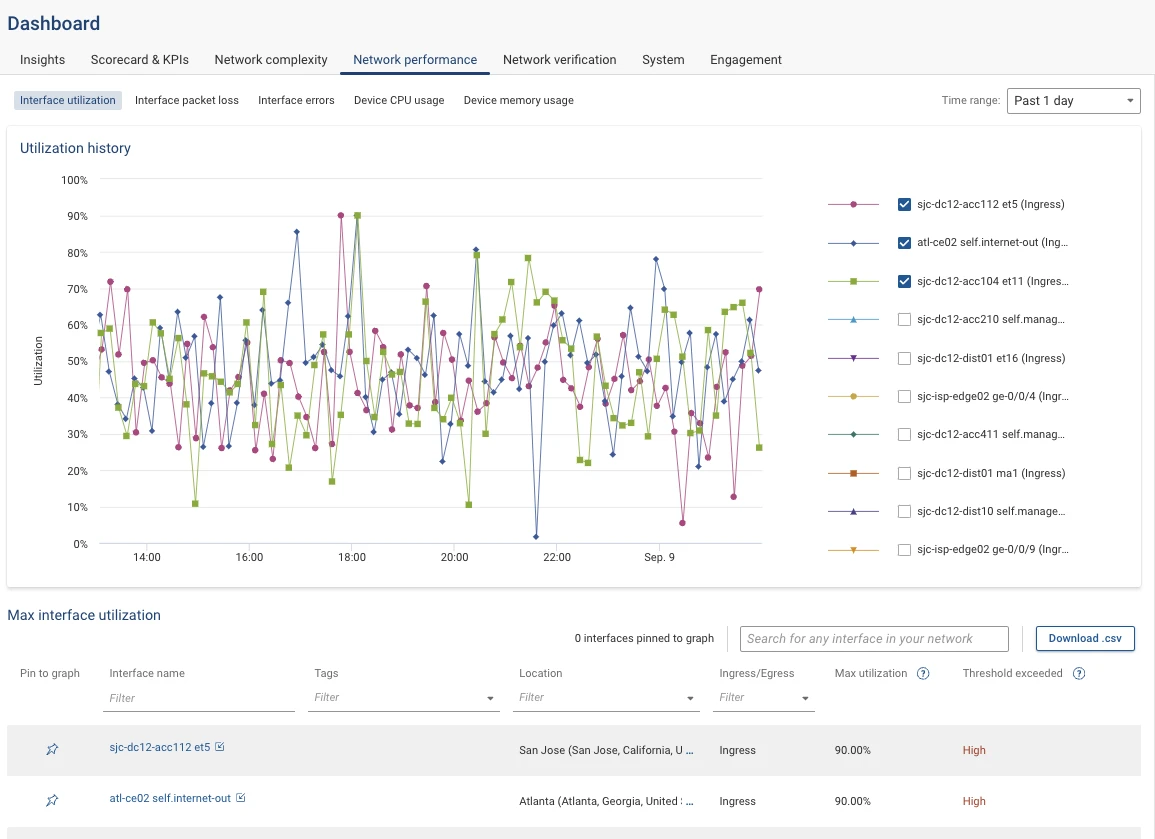
Forward Enterprise collects performance statistics via SNMP, covering device-level and interface-level metrics including CPU utilization, memory consumption, and interface data.
Capabilities:
- Real-time device and interface health metrics available on demand
- Historical performance trend data over 24-hour and 7-day periods
- Performance data integrated into path analysis results for both devices and individual ingress/egress interfaces
- Time-series charting for trend analysis and capacity assessment
Firewall Rule Reporting and Analysis
Forward Enterprise provides direct firewall rule reporting and analysis through NQE library queries and lifecycle-aware ACL datasets in the unified network model.
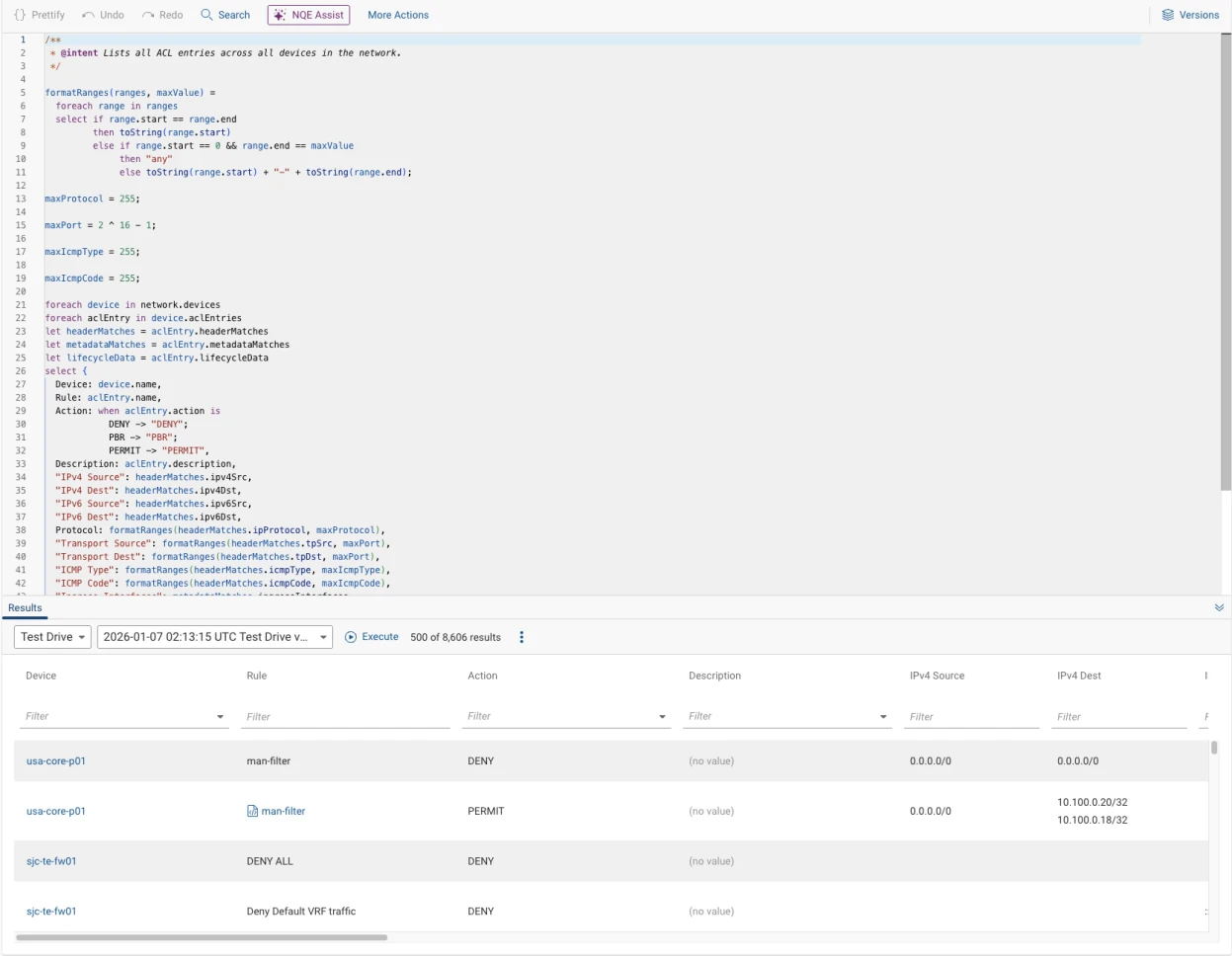
The ACL Entries NQE query provides rule-level reporting across devices, including action, source/destination match criteria, ingress/egress interfaces, and lifecycle fields (created, last modified, last used, hit count).
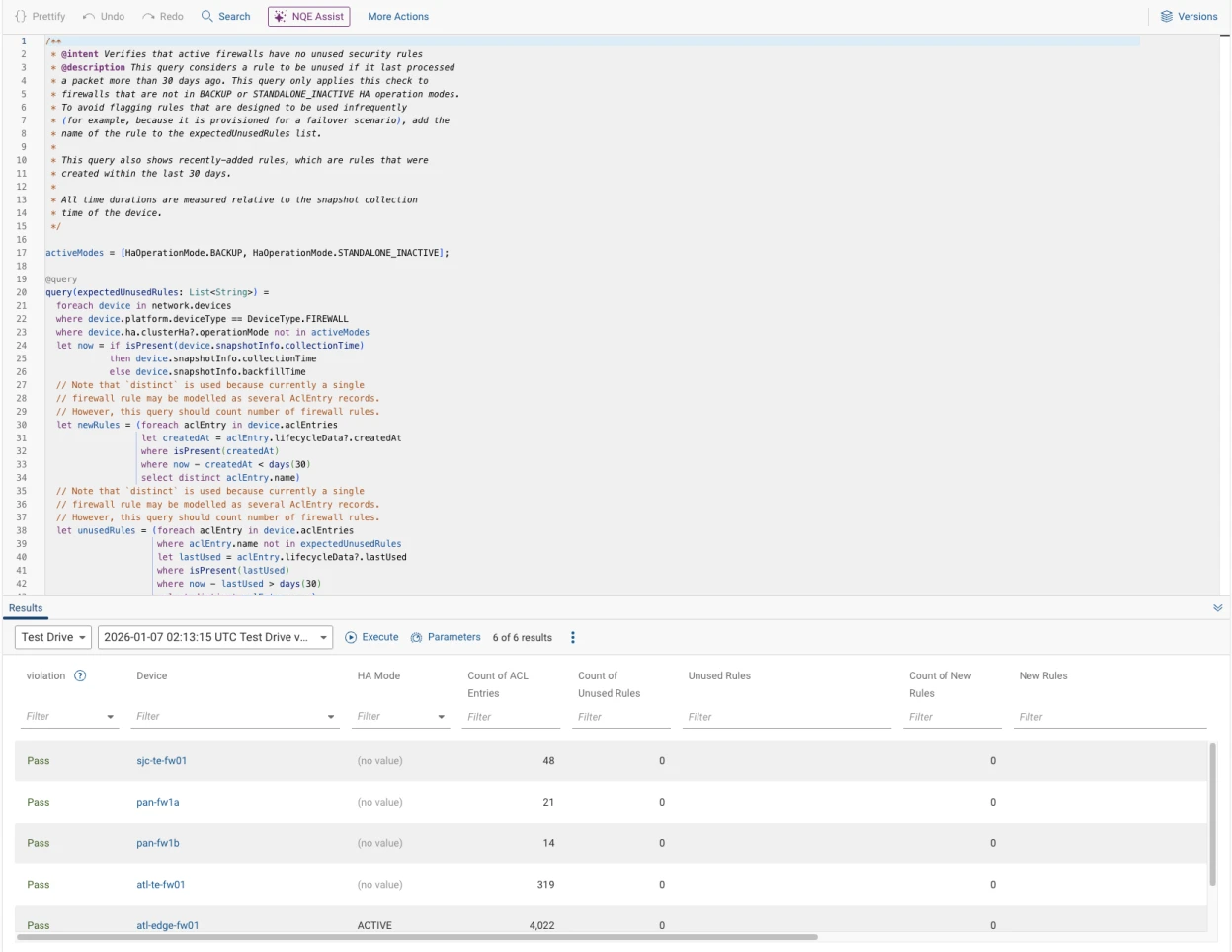
The Firewalls with Unused Security Rules NQE query identifies active firewalls with rules unused for more than 30 days while also surfacing recently added rules.
Security posture, path analysis, and diffs remain complementary controls for validating enforcement points and detecting policy-impacting changes. The query logic is reusable for reports, recurring verification checks, and audit evidence exports.